Understanding Insider Risk
Modern organizations rely heavily on digital systems, cloud platforms, and shared data environments. Employees access business applications, customer records, intellectual property, and internal documents every day. This access is essential for productivity and collaboration. However, it also introduces a category of cybersecurity exposure known as insider risk.
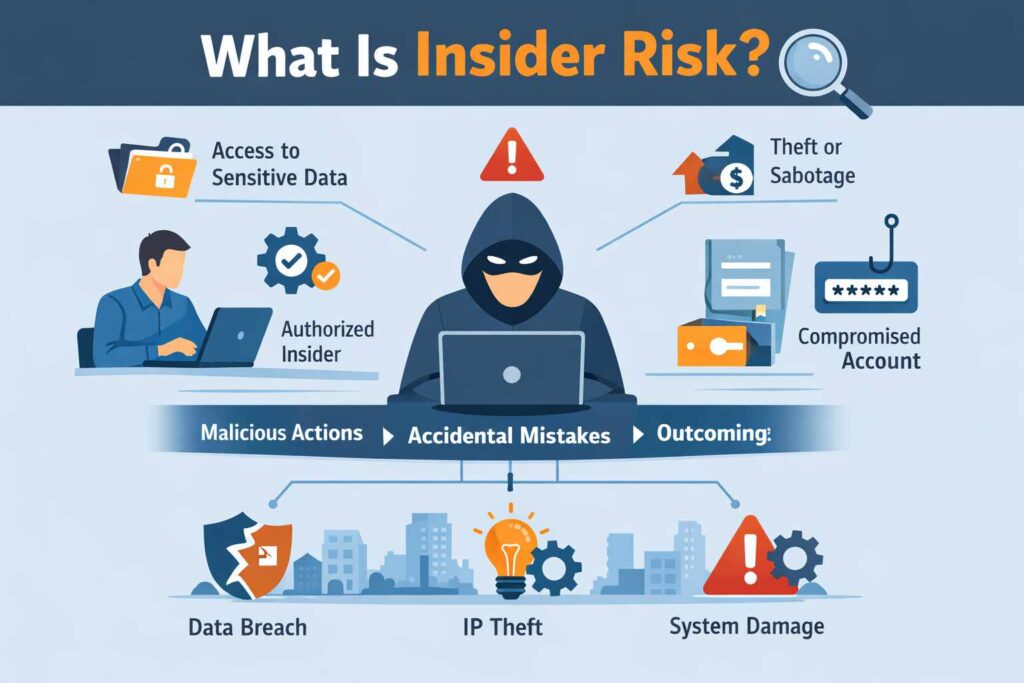
Insider risk refers to the potential damage that may occur when individuals inside an organization misuse their legitimate access to systems, data, or infrastructure. Unlike traditional cyber attacks that originate outside the organization, insider risk emerges from people who already operate within the trusted environment of the enterprise.
Because insiders already have credentials and permissions, their actions can be difficult to distinguish from normal business activity. Security teams must therefore detect subtle behavioral changes rather than obvious system intrusions. This complexity makes insider risk one of the most challenging areas of cybersecurity.
Understanding insider risk is the first step toward building an effective protection strategy. Organizations that recognize this risk early are better positioned to protect sensitive data, maintain operational stability, and preserve customer trust.
What Is Insider Risk
Insider risk exists whenever individuals with authorized access interact with organizational systems. This access may allow them to view, modify, transfer, or store sensitive information. While most employees use this access responsibly, the same permissions can create opportunities for misuse.
Individuals who may contribute to insider risk include employees, contractors, third party vendors, consultants, and even former employees who still retain active credentials. Each of these individuals interacts with corporate systems for legitimate reasons. However, their actions can unintentionally or deliberately expose the organization to security incidents.
One of the defining characteristics of insider risk is that the individual does not need to bypass security defenses. The access already exists. Instead of breaking into systems, the insider simply uses legitimate permissions in ways that were not intended or approved.
For example, an employee might download sensitive customer records to a personal device for convenience. A contractor may copy internal project files before leaving an engagement. In both situations the individuals already had authorized access. The risk emerges from how that access is used.
This reality forces organizations to rethink traditional cybersecurity strategies. Instead of focusing only on blocking external attackers, security teams must also monitor how internal access is used across systems and data environments.
Why Insider Risk Is Difficult to Detect
Insider risk presents unique detection challenges because the activity often appears legitimate. Most cybersecurity tools were originally designed to identify external threats such as malware infections, network intrusions, or unauthorized login attempts.
Insider activity is different. The individual logs in with valid credentials and performs actions that appear similar to normal work tasks. Downloading files, accessing databases, or opening internal documents may all be part of routine responsibilities.
This similarity between legitimate activity and suspicious behavior makes detection difficult. Security teams must analyze patterns of behavior rather than individual events. For example, an employee downloading a document may be normal. However, downloading thousands of sensitive files late at night may indicate unusual behavior.
Another challenge arises from the level of trust organizations place in their workforce. Employees are expected to collaborate, share information, and work efficiently. Excessive monitoring can disrupt productivity or raise privacy concerns. As a result, organizations must carefully balance security visibility with employee trust.
Because of these challenges, insider incidents often remain undetected for long periods. By the time they are discovered, sensitive data may already have been exposed or stolen.
Accidental Insider Risk
Not all insider incidents involve malicious intent. In many cases the damage occurs because of human error or poor security awareness. Employees may unintentionally create security vulnerabilities while attempting to complete everyday tasks.
For example, an employee might accidentally send confidential documents to the wrong email recipient. Another employee may store company files on a personal cloud storage service without realizing the security implications. Misconfigured access permissions in shared folders can also expose sensitive data to unauthorized individuals.
Phishing attacks represent another common source of accidental insider risk. Attackers may send convincing emails that trick employees into revealing login credentials or downloading malware. Once attackers gain access to those credentials, they can operate inside the network while appearing to be legitimate users.
Although these incidents are unintentional, their consequences can be serious. Data breaches caused by human error can trigger regulatory penalties, customer distrust, and financial losses.
Organizations must therefore treat accidental insider risk as a significant security concern rather than dismissing it as simple human mistakes.
Malicious Insider Risk
In contrast to accidental incidents, malicious insider risk occurs when individuals intentionally misuse their access privileges. These individuals deliberately exploit their position within the organization to steal data, sabotage systems, or gain personal benefits.
Motivations for malicious insider activity vary widely. Financial gain is one of the most common drivers. Employees may attempt to sell customer databases, proprietary designs, or confidential research to competitors or criminal groups.
Workplace dissatisfaction can also motivate malicious behavior. Disgruntled employees who feel unfairly treated may attempt to damage systems or leak sensitive information as a form of retaliation.
In some cases, insiders act on behalf of external organizations or foreign entities seeking valuable corporate intelligence. These activities may involve stealing product designs, research findings, or strategic business plans.
Because malicious insiders understand internal processes and security controls, they can be particularly dangerous. Their knowledge allows them to navigate systems more effectively than external attackers.

Insider Risk vs Insider Threat
The terms insider risk and insider threat are frequently used interchangeably, but they describe different stages of the same problem. Insider risk refers to the possibility that individuals with legitimate access could cause harm to the organization. It represents the conditions that allow harmful actions to occur.
Insider threat refers to the moment when that potential risk becomes a real security incident. When an employee steals confidential data or sabotages systems, the insider risk has evolved into an insider threat.
Understanding this distinction helps organizations develop proactive security strategies. If security teams focus only on responding to insider threats after they occur, the damage may already be extensive. A more effective approach involves identifying risk indicators early and reducing the likelihood that those risks will turn into active threats.
This approach is known as insider risk management. It involves monitoring behavioral patterns, controlling access privileges, and educating employees about responsible data handling practices.
The Growing Importance of Insider Risk Awareness
Insider risk has gained increased attention in recent years as organizations adopt cloud computing, remote work environments, and distributed digital infrastructure. Employees now access corporate systems from multiple locations and devices. While this flexibility improves productivity, it also increases the complexity of monitoring system activity.
At the same time, organizations are generating more data than ever before. Sensitive information flows through collaboration platforms, cloud storage systems, and enterprise applications. The greater the volume of data available, the greater the potential impact of insider incidents.
Industry research also suggests that insider related incidents are becoming more common. Analysis discussed in the 2026 Insider Risk Report: The Year AI Became an Insider highlights how organizations are recognizing insider activity as a growing cybersecurity concern. Additional industry coverage referenced in a PR Newswire announcement indicates that many organizations report experiencing insider related security incidents.
These trends demonstrate why insider risk management must become a central component of modern cybersecurity strategies. Organizations can no longer assume that threats originate only from outside their networks.
Preparing for the Next Stage
Understanding insider risk provides the foundation for building stronger cybersecurity defenses. Organizations must recognize that internal access can create vulnerabilities if it is not carefully managed.
The next step involves examining the different types of insider threats and understanding how they operate within modern enterprises. By identifying the behaviors and motivations associated with insider threats, security teams can develop more effective detection and prevention strategies.
In the next section, we will explore the primary categories of insider threats and examine how they affect organizations across industries.

Types of Insider Threats
Understanding insider risk requires a closer look at the different ways insider activity can develop into real security incidents. Not every insider threat looks the same. Some originate from deliberate actions, while others occur because employees unknowingly expose the organization to risk.
Security professionals generally categorize insider threats into three primary groups. These categories help organizations understand motivations, identify behavioral patterns, and design appropriate prevention strategies. The three most widely recognized forms are malicious insiders, negligent insiders, and compromised insiders.
Each category presents different challenges for cybersecurity teams. Some threats involve intentional misuse of access privileges, while others arise from simple human mistakes. In many cases, attackers outside the organization exploit legitimate user accounts, creating threats that appear to originate internally.
Recognizing these distinctions is essential for effective insider risk management. Organizations that understand how insider threats emerge are better equipped to detect suspicious behavior early and prevent incidents before they escalate.
Malicious Insider Threat
A malicious insider is an individual who intentionally misuses authorized access to harm the organization. This type of insider threat is often the most damaging because the individual already understands the internal structure of the organization.
Malicious insiders may know where sensitive data is stored, how security controls operate, and which systems are critical to daily operations. This knowledge allows them to bypass defenses more easily than external attackers.
The motivations behind malicious insider behavior vary widely. Financial gain is one of the most common reasons. An employee might steal customer databases or proprietary information and sell it to competitors or criminal organizations.
Another motivation is workplace dissatisfaction. Employees who feel unfairly treated or overlooked may attempt to retaliate against the organization. In extreme cases, disgruntled insiders may sabotage systems, delete critical files, or leak confidential data to the public.
Corporate espionage is another serious concern. In some industries, insiders may be recruited by competitors or foreign entities to obtain sensitive research data, product designs, or strategic business plans. These incidents can undermine years of investment and weaken an organization’s competitive position.
Because malicious insiders intentionally attempt to avoid detection, their activities can be difficult to identify. They may carefully disguise their actions as routine tasks or slowly exfiltrate data over long periods of time.
This makes behavioral monitoring and access control critical components of insider threat protection.
Negligent Insider Threat
Not every insider incident involves malicious intent. In many organizations, the most common security issues arise from simple human error. These cases are known as negligent insider threats.
Negligent insiders do not intend to harm the organization. Instead, they create security vulnerabilities through careless behavior, lack of awareness, or failure to follow security policies.
For example, an employee might reuse the same password across multiple accounts. If attackers obtain that password through a phishing attack, they could gain access to internal systems without triggering traditional security alerts.
Employees may also share login credentials with colleagues for convenience. While this practice may seem harmless, it removes accountability and makes it difficult to trace system activity during security investigations.
Another common issue involves improper handling of sensitive data. Employees sometimes download corporate documents to personal devices or store them on unsecured cloud platforms to make remote work easier. These actions may expose confidential information to unauthorized access.
Email mistakes also contribute to negligent insider risk. Sending sensitive documents to the wrong recipient or attaching confidential files to unsecured email messages can quickly create data exposure incidents.
The challenge with negligent insider threats is that they occur frequently and often appear harmless at first. However, when sensitive information is involved, even small mistakes can lead to significant security consequences.
Organizations must therefore invest in employee awareness programs and clear security policies that help reduce these risks.
Compromised Insider Threat
A compromised insider threat occurs when an external attacker gains control of a legitimate user account. In these situations, the attacker operates within the organization’s network while appearing to be a trusted employee.
This type of attack often begins with credential theft. Attackers may use phishing emails, malware, or social engineering techniques to trick employees into revealing login information.
Once attackers gain access to valid credentials, they can move through systems without triggering traditional intrusion alerts. Security systems may interpret the activity as legitimate user behavior.
Compromised accounts are particularly dangerous when they belong to employees with privileged access. Administrative accounts often control critical systems, databases, or security configurations. If attackers obtain these credentials, they may gain extensive control over organizational infrastructure.
Another risk involves session hijacking. In these attacks, criminals intercept active user sessions and take control of authenticated connections without needing login credentials.
Because compromised insider threats appear to originate from legitimate users, detecting them requires advanced behavioral monitoring and identity protection technologies.
Organizations must continuously analyze user behavior to identify anomalies such as unusual login locations, abnormal access patterns, or unexpected data transfers.
Why Insider Threats Are Increasing
The frequency of insider related incidents has increased in recent years. Several technological and organizational factors contribute to this trend.
Digital transformation has expanded the number of systems and platforms employees use daily. Cloud services, collaboration platforms, and remote access tools allow employees to work from virtually anywhere. While these technologies improve efficiency, they also create new security challenges.
Remote work environments present additional risks. Employees may access corporate systems from home networks, personal devices, or public internet connections. These environments often lack the security controls found within corporate networks.
Organizations also manage significantly larger volumes of data than in previous decades. Sensitive information flows through email systems, shared drives, cloud storage platforms, and enterprise applications. The greater the volume of accessible data, the greater the potential impact of insider incidents.
Research findings discussed in the 2026 Insider Risk Report: The Year AI Became an Insider highlight how organizations are increasingly recognizing insider activity as a growing cybersecurity concern. Industry reporting referenced in a PR Newswire announcement also suggests that a large percentage of organizations have experienced insider related security incidents.
These trends indicate that insider threats are no longer isolated cases. They represent a persistent challenge that requires structured prevention strategies.
The Importance of Early Detection
Detecting insider threats early is critical for minimizing damage. The longer insider activity continues undetected, the greater the potential impact on the organization.
Security teams must therefore focus on identifying behavioral signals that indicate elevated risk. These signals may include unusual login times, access to systems outside an employee’s job responsibilities, or large volumes of data transfers.
Early detection allows organizations to investigate suspicious behavior before sensitive information is compromised. In many cases, identifying risk indicators early can prevent incidents from escalating into full security breaches.
This proactive approach forms the foundation of modern insider risk management programs.
Preparing for the Next Stage
Understanding the different types of insider threats helps organizations recognize how insider incidents develop. Malicious insiders, negligent insiders, and compromised accounts each present unique risks that require different detection strategies.
However, recognizing these threats is only one part of the challenge. Organizations must also understand the broader consequences of insider incidents and how they affect operations, finances, and reputation.
In the next section, we will examine how insider risk impacts organizations and why effective insider threat protection has become a critical component of modern cybersecurity strategy.

How Insider Risk Impacts Organizations
Insider risk is not simply a technical cybersecurity issue. When insider incidents occur, their impact often extends far beyond the security team. The consequences can affect financial performance, operational stability, regulatory compliance, and the overall reputation of the organization.
Because insiders already have access to internal systems, the damage they can cause is often deeper than that of external attackers. An external attacker typically needs time to explore systems after gaining access. Insiders already know where valuable information is stored and how internal processes operate.
For this reason, insider related incidents frequently lead to severe and long lasting consequences. Organizations that underestimate insider risk may find themselves dealing with data exposure, intellectual property loss, or operational disruptions that take months or even years to recover from.
Understanding these potential impacts helps leadership teams recognize why insider risk management should be treated as a core component of cybersecurity strategy.
Data Breaches and Exposure of Sensitive Information
One of the most immediate consequences of insider incidents is the exposure of sensitive data. Modern organizations store enormous volumes of information, including customer records, financial documents, internal communications, and proprietary research.
When insiders misuse their access privileges, they may unintentionally or deliberately expose this information. For example, an employee might download confidential files to a personal device, share internal documents with unauthorized individuals, or transfer large volumes of data outside the organization.
In malicious cases, insiders may intentionally steal sensitive information for financial gain or competitive advantage. This could involve copying product designs, customer databases, strategic business plans, or research results.
Once sensitive data leaves the organization’s control, the consequences can escalate quickly. Stolen information may appear on underground marketplaces or be shared with competitors. Even accidental exposures can trigger serious regulatory investigations and legal liabilities.
For organizations operating in regulated industries such as finance, healthcare, or telecommunications, data breaches can lead to significant penalties and compliance violations.
Loss of Intellectual Property
Intellectual property often represents one of the most valuable assets an organization possesses. Technology companies, manufacturing firms, pharmaceutical organizations, and research institutions invest enormous resources into developing proprietary innovations.
Insider incidents can threaten these investments. Employees who have access to product designs, engineering blueprints, software code, or scientific research may copy or transfer this information outside the organization.
In some cases, individuals who plan to join competing companies attempt to take valuable information with them. This behavior can provide competitors with insights into product development strategies, pricing models, or technological innovations.
The theft of intellectual property can weaken an organization’s competitive advantage and undermine years of research and development. Once proprietary information becomes available outside the organization, it may be impossible to fully recover or control its distribution.
For industries driven by innovation, intellectual property theft represents one of the most damaging forms of insider threat.
Operational Disruption
Insider incidents can also disrupt daily business operations. Employees with privileged access to systems may have the ability to modify configurations, delete files, or interfere with critical infrastructure.
Even small changes to system settings can create significant operational challenges. For example, altering access permissions in a shared database may prevent employees from performing essential tasks. Deleting system files could cause applications to stop functioning.
In more severe cases, malicious insiders may intentionally sabotage infrastructure. A system administrator with extensive privileges could disable monitoring systems, remove backups, or alter production systems.
Operational disruptions can affect manufacturing processes, customer service platforms, and financial transactions. The resulting downtime can lead to lost revenue, delayed services, and damage to customer relationships.
Even when incidents are accidental, the recovery process may require extensive technical investigation and system restoration efforts.
Financial Consequences
The financial impact of insider incidents can be substantial. Organizations must often allocate significant resources to investigate security incidents, restore compromised systems, and strengthen security controls.
Incident response efforts may involve cybersecurity specialists, legal advisors, and compliance experts. These investigations can be complex and time consuming, particularly when sensitive data has been exposed.
Additional costs may arise from regulatory fines, customer compensation programs, and legal settlements. In some cases, organizations must notify affected customers and provide credit monitoring services or identity protection support.
Operational disruptions caused by insider incidents may also lead to lost productivity and missed business opportunities. If systems remain unavailable for extended periods, organizations may experience significant revenue losses.
When these financial factors combine, insider incidents can become extremely expensive events.
Damage to Reputation and Trust
Beyond financial losses, insider incidents can significantly affect an organization’s reputation. Customers, partners, and investors expect organizations to protect sensitive information and maintain reliable services.
When insider incidents become public, stakeholders may question whether the organization has effective security controls in place. News of data breaches or intellectual property theft can damage public confidence and create long term trust issues.
Reputation damage can also affect customer loyalty. Organizations that fail to protect customer data may lose clients who seek more secure alternatives. Investors may also reconsider their support if security weaknesses appear to threaten the organization’s stability.
Rebuilding trust after a major security incident requires transparency, improved security practices, and sustained communication with stakeholders.
Legal and Regulatory Challenges
Insider incidents can trigger serious legal and regulatory consequences. Many countries enforce strict data protection laws that require organizations to safeguard personal and financial information.
If insider actions lead to the exposure of regulated data, organizations may face investigations from government authorities or industry regulators. These investigations often require detailed reporting about how the incident occurred and what measures are being implemented to prevent similar events.
Organizations may also face lawsuits from affected customers or partners. Legal disputes can become lengthy and expensive, particularly if sensitive personal data was involved.
In highly regulated industries such as banking, healthcare, and telecommunications, compliance failures can lead to significant financial penalties and operational restrictions.
These legal consequences further highlight the importance of proactive insider risk management.
The Long Term Organizational Impact
Insider incidents rarely affect only a single department. Their consequences often spread throughout the organization and influence multiple areas of operation.
Security teams must investigate the incident and implement corrective controls. IT teams may need to rebuild systems or restore compromised data. Legal teams must evaluate regulatory obligations and potential liabilities. Leadership teams must address communication with customers, partners, and investors.
This coordinated response can consume significant organizational resources. Even after systems are restored, the organization may need to redesign security processes or implement new monitoring technologies.
The long term impact of insider incidents therefore extends far beyond the initial security event.
The Importance of Proactive Risk Management
Given the wide range of potential consequences, organizations cannot afford to treat insider incidents as rare or isolated events. Instead, they must adopt proactive strategies that focus on identifying and managing insider risk before harmful activity occurs.
Proactive insider risk management includes monitoring user behavior, limiting unnecessary access privileges, and strengthening employee awareness programs. By identifying unusual patterns early, security teams can intervene before incidents escalate.
Industry research continues to highlight the growing importance of these strategies. Insights discussed in the 2026 Insider Risk Report emphasize that insider related incidents are becoming more common as organizations adopt new technologies and digital collaboration environments.
These trends reinforce the need for organizations to treat insider risk management as a continuous security discipline rather than a reactive response to isolated incidents. Organizations that want deeper visibility into user behavior and access activity often adopt dedicated insider risk management platforms designed to detect abnormal patterns and identify emerging threats early.
Moving Forward
Understanding the impact of insider risk provides important context for why organizations must invest in prevention strategies. Data breaches, operational disruptions, financial losses, and reputation damage all demonstrate the seriousness of insider threats.
However, recognizing these risks is only part of the solution. Organizations must also understand the factors that are driving the growth of insider incidents in modern digital environments.
In the next section, we will explore the technological and organizational changes that are increasing insider risk and examine why this challenge continues to evolve across industries.


