Understanding how ransomware industry works is critical for organizations facing modern cyber threats. Ransomware is no longer a single attacker problem. Instead, it has evolved into a structured ecosystem with defined roles, financial incentives, and operational workflows.
Today, ransomware groups operate with efficiency similar to legitimate enterprises. They use collaboration models, service offerings, and revenue sharing. As a result, attacks have become more scalable and harder to defend against. Therefore, organizations must understand this industry from a strategic perspective.
What Is How Ransomware Industry Works
The concept of how ransomware industry works describes the organized ecosystem behind ransomware attacks. This ecosystem includes developers, affiliates, access brokers, and negotiation specialists.
Each actor plays a specific role. Developers create ransomware payloads and infrastructure. Affiliates execute attacks using these tools. Meanwhile, brokers sell initial access to compromised networks.
This division of labor increases efficiency. In addition, it lowers the barrier to entry for attackers. As a result, ransomware campaigns continue to grow in scale and complexity.
Why It Is Critical
This issue is critical because ransomware directly impacts operations, finances, and reputation. Organizations often face downtime, data loss, and regulatory consequences.
Moreover, attackers now use multiple extortion techniques. They encrypt systems and threaten to leak sensitive data. Therefore, victims face pressure from both operational disruption and public exposure.
In addition, ransomware attacks increasingly target critical sectors. Healthcare, finance, and infrastructure remain high value targets. As a result, the broader economic impact continues to rise.
Step by Step Breakdown of How Ransomware Industry Works
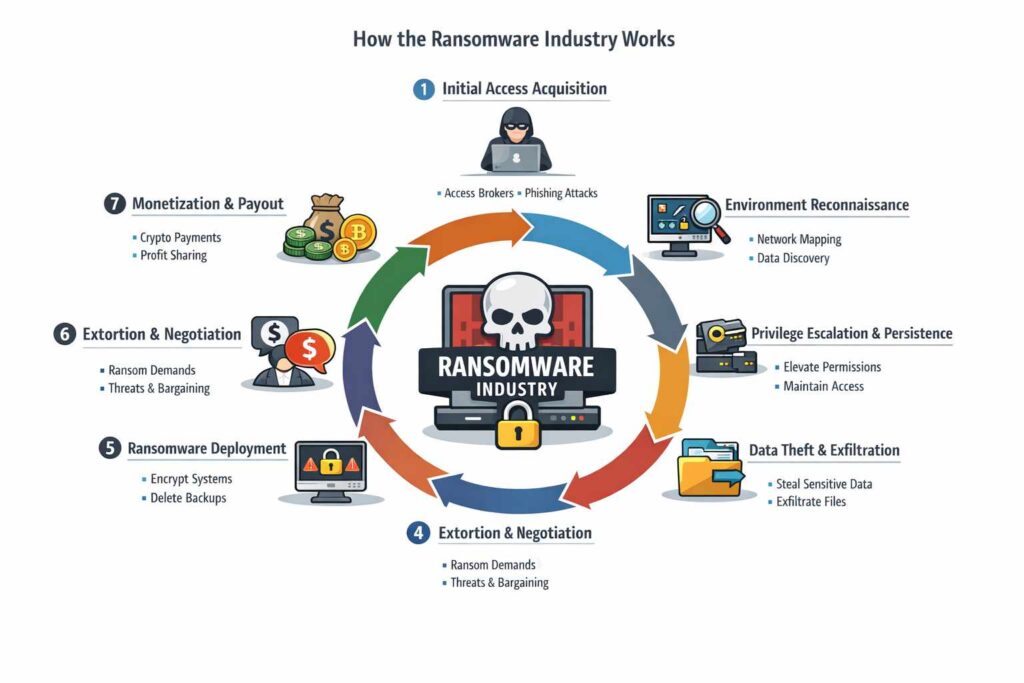
To fully understand how ransomware industry works, it is important to analyze the lifecycle in stages. Each stage represents a distinct risk point and operational function.
Step 1 Initial Access Acquisition
The process begins with gaining access to a target environment.
Threat actors often obtain access through intermediaries known as access brokers. These brokers sell credentials or entry points to ransomware groups.
In other cases, affiliates gain access through phishing or exposed services. However, the key point is that access is often commoditized.
This stage introduces risk because attackers already operate inside the environment before detection.
Step 2 Environment Reconnaissance
After access, attackers study the environment.
They identify critical systems, backup locations, and sensitive data stores. In addition, they map user privileges and network structure.
This phase allows attackers to plan their next move carefully. Therefore, they minimize noise and avoid early detection.
Step 3 Privilege Expansion and Persistence
Next, attackers expand their access.
They move from initial entry points to more critical systems. At the same time, they establish persistence to maintain long term access.
This ensures that even if one access point is removed, others remain active. As a result, attackers maintain control over the environment.
Step 4 Data Collection and Exfiltration
Before deploying ransomware, attackers often collect sensitive data.
This includes intellectual property, financial records, and personal information. They may transfer this data to external infrastructure.
This step supports double extortion strategies. Therefore, even if recovery is possible, data exposure remains a threat.
Step 5 Ransomware Deployment
Once preparation is complete, attackers deploy ransomware.
The payload encrypts systems and disrupts operations. In addition, it may target backups to prevent recovery.
At this stage, the organization experiences immediate impact. Therefore, response time becomes critical.
Step 6 Extortion and Negotiation
After encryption, attackers initiate communication.
They demand payment in exchange for decryption and data protection. In many cases, negotiation specialists handle this process.
These actors use psychological pressure and deadlines. As a result, victims face difficult decisions under stress.
Step 7 Monetization and Revenue Sharing
Finally, payments are processed through cryptocurrency systems.
The revenue is shared among participants. Developers receive a portion, while affiliates keep a percentage.
This model incentivizes continued activity. Therefore, ransomware remains a profitable and persistent threat.
Detection Challenges
Detecting ransomware operations is difficult due to their structured approach.
First, attackers operate quietly during early stages. Reconnaissance and lateral movement generate minimal alerts.
Second, legitimate tools are often used to avoid detection. This makes activity appear normal within the environment.
In addition, encryption occurs quickly once triggered. Therefore, detection windows are limited.
As a result, many organizations detect ransomware only after significant damage occurs.
Why Traditional Defenses Fail
Traditional defenses focus on perimeter security. However, ransomware attacks often begin inside the network.
Once attackers gain access, they bypass external controls. In addition, trusted credentials reduce suspicion.
Moreover, signature based detection struggles with evolving ransomware variants. Attackers frequently modify their tools.
Therefore, traditional models fail to address modern ransomware tactics.
Mitigation Strategies
Organizations must adopt layered defenses to address how ransomware industry works.
First, implement strong access controls. Limit privileges and monitor credential usage.
Second, use continuous monitoring and behavioral analytics. This helps detect unusual activity early.
Third, maintain secure and isolated backups. Ensure that recovery remains possible without paying ransom.
In addition, conduct regular security assessments. Identify vulnerabilities before attackers exploit them.
Finally, train employees to recognize phishing and social engineering attempts. Human awareness reduces initial access risks.
Broader Security Implications
The ransomware industry affects the entire cybersecurity landscape.
It drives the growth of underground economies. In addition, it encourages collaboration among threat actors.
Moreover, it increases pressure on organizations to invest in security. Regulatory bodies also respond with stricter requirements.
As a result, ransomware shapes both defensive strategies and policy decisions.
What Organizations Should Do Now
Organizations should take immediate action to reduce exposure.
First, assess current security posture and identify gaps.
Second, implement zero trust principles to limit access.
Third, improve incident response capabilities. Teams must respond quickly to minimize damage.
In addition, engage with threat intelligence sources to stay informed. Structured frameworks and validation models can support consistent analysis and response .
Finally, leadership must prioritize cybersecurity as a core business function.
Conclusion
Understanding how ransomware industry works provides valuable insight into modern cyber threats. This industry operates with structure, efficiency, and financial motivation.
Each stage of the lifecycle introduces risk. From initial access to monetization, attackers exploit weaknesses systematically.
Therefore, organizations must adopt proactive and layered defenses. Strong governance, monitoring, and awareness remain essential.
FAQ
What is how ransomware industry works
It refers to the structured ecosystem of ransomware operations, including developers, affiliates, and monetization models.
Why is ransomware so successful
Ransomware succeeds due to its organized business model and ability to scale attacks through affiliates and shared tools.
How do ransomware groups make money
They generate revenue through ransom payments, often using cryptocurrency and revenue sharing models.
How can organizations defend against ransomware
Organizations should use strong access controls, continuous monitoring, secure backups, and employee training.


